One minute, you are minding your own business, surfing the web. Then suddenly an alert pops up on your screen: “VIRUS DETECTED! CALL THE NUMBER BELOW IMMEDIATELY!” followed by a plethora of other pop-ups and possibly an audio transcription of the messages. Though it may pretend to be antivirus software, it is actually a pop-up of scareware, “a cyberattack tactic that scares people into visiting spoofed or infected websites or downloading malicious software” (Fortinet).
Scareware started off causing “minor damage, scamming victims out of a few dollars for useless bloatware. Today, scareware has become a vector for nastier cyberthreats like ransomware” (IBM). Bloatware is software that is, generally, useless and serves no purpose but to take up space. In a way, scareware is “the gateway to a more intricate cyberattack and not an attack in and of itself” (Crowdstrike). This is due to how scareware is often used to phish financial information from unsuspecting users by selling “a fake antivirus software that does nothing or turns out to be malware”, such as a Trojan Horse (IBM). While some do still spread scareware genuinely meant to scare people, it is almost always done as a genuine attempt to gain access to a user’s machine, financial information, or more.
How Does Scareware Work?
Scareware mainly “operates through social engineering—a tactic that manipulates users into making rushed actions based on fear” (Malwarebytes). This may include pop-ups that will not go away and urge you to call a certain number, fake antivirus alerts, audio recordings that claim viruses were detected, and similar. Whatever scammers can do to scare a victim, they will do; scareware “preys on people’s natural fear of viruses and other security risks. By making a victim feel like their device is in immediate danger, it pushes them to act without thinking things through, which is exactly what the scammers want” (Malwarebytes).
This is why it is always important to slow down before making any sort of decision when it comes to responding to a strange pop-up on your computer. Many types of scareware aim “to scare people into paying for software that purportedly provides a quick fix to the ‘problem’”, so by slowing down and not letting the scareware frighten you, you can avoid losing both money and time (Fortinet). Other than pop-ups, scareware can also be “distributed by spam email, through messages that trick people into buying worthless items or services” (Fortinet).
Malwarebytes highlights three key features that most, if not all, types of scareware contain:
Here are a few characteristics that set scareware pop-ups apart from legitimate warnings:
Aggressive language: Real security software typically uses neutral language. If a message seems overly urgent or threatening, it’s likely to be scareware.
Unusual behavior: Scareware pop-ups often lack an obvious way to close them. Clicking “Cancel” or even the “X” button may trigger more pop-ups instead.
Fake branding: Some pop-ups might display logos that look similar to well-known antivirus companies, but subtle details are off, indicating they’re not authentic.
Malwarebytes
While Malwarebytes includes urgency under the category of aggressive language, Fortinet states that it is, in itself, its own key feature of scareware. Threat actors will “attempt to convince users that the supposed device problem requires immediate action and then prompt them to install the program as quickly as possible. Therefore, always be careful with any ad that demands the user to act immediately. It is most likely scareware” (Fortinet). If you do click on the pop-up or advertisement, you will likely be “inadvertently and unknowingly downloading malicious programs, such as malware, ransomware, spyware, a virus or a Trojan” onto your device, which will cause further harm (Crowdstrike).
How to Remove Scareware
Of course, accidents always happen, so it is important to know how to remove scareware from your device if it gets infected. In some cases, scareware itself is just a pop-up that takes up the whole screen, with the close or “X” button being “difficult to find and show[ing] even more fake warnings when the user manages to locate and click on it” or “a covert drive-by download” (Fortinet; IBM). The best way to close out of these is “with the Control-Alt-Delete command on a Windows device and Command-Option-Escape to open the Force Quit window on a Mac device” (Fortinet). Pressing these keys will open a window that will show running processes and apps; right click on the web browser and select the close option. In the event that this does not work, you can simply power down your computer by pressing and holding the power button, which should close out of the browser and anything else that opened on your device.
However, in some cases- such as if a victim mistakenly clicked on or downloaded anything from the scareware- it can be a bit harder to get rid of. Some types of scareware “can disable other security software and hide program files, making them harder to detect. Some fake antivirus software has been known [to] reinstall itself after removal” (IBM). These traits make it much harder to remove the scareware since it will either keep reinstalling itself onto your computer or hiding itself away so that it can re-add itself later. According to Fortinet, more persistent types of scareware “can be removed using a software tool that removes malware and all signs of a virus infection. The original antivirus software that was bypassed or disabled by the scareware also needs to be re-installed and patched” (Fortinet).
Crowdstrike outlines the following steps to take if your device is infected with scareware:
If scareware has infected your device, begin by following these general steps to remove it and secure your system.
Disconnect from the internet. This step stops any further data transmission and prevents additional malicious downloads.
Run a full system scan with your security software. Make sure the software is kept up-to-date so that it can effectively detect and quarantine the latest scareware or any other malware threats.
Clear your browser’s cache, history, and cookies. Scareware often leaves traces in your browser that can trigger further deceptive pop-ups. Resetting the browser can help remove these remnants.
After these general steps, proceed with the specific removal methods for your operating system.
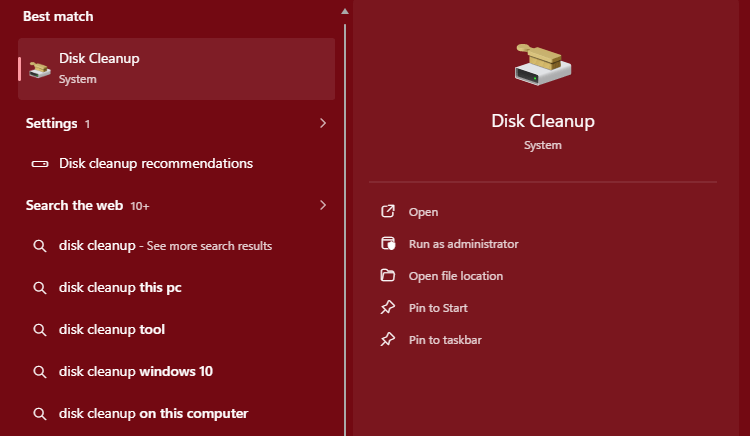
Scareware removal steps for Windows
Reboot your device in Safe Mode by restarting and pressing F8 (or Shift+Restart) before Windows loads. Select “Safe Mode” from the list of options.
Go to “Control Panel” and then “Programs and Features” to review your installed software. Uninstall any unfamiliar or suspicious programs.
Open your browser and reset its settings to default. This will remove any changes scareware may have made to your homepage, extensions, or toolbars.
Scareware removal steps for Mac
Restart your device while holding down the Shift key until you see the Apple logo. This will boot your Mac into Safe Mode, limiting the programs that load on startup.
Open the “Applications” folder and review the list of installed programs. If you see any suspicious software, drag it to the Trash and then empty the Trash to fully remove the files.
Open your browser, go to settings, and restore the default settings. This will remove any scareware-related changes, including altered search engines and added toolbars.
These steps should help you effectively remove scareware from your device, whether you’re using Windows or Mac. Regular scans with your security software can further help to keep your device secure and prevent future infections.” (Malwarebytes)
“In the event of a scareware attack, users should also take extra steps to safeguard against potentially compromised information. This may include:
Changing passwords or other long-in credentials
Performing a scan on other personal devices to ensure they were not inadvertently compromised
Requesting new credit cards from your bank or financial institution
Periodically checking your credit report to ensure you were not the victim of fraud or identity theft.
Crowdstrike
How to Stay Safe from Scareware
Since there are different ways that scareware is delivered- via pop-up, website, or email- there are a few different methods to stay safe and avoid it. Blocking pop-ups in your web browser can help prevent many types of scareware from appearing; even though “pop-up blockers won’t catch everything, they add an extra layer of security” (Malwarebytes). Additionally, some opt to install adblocker extensions onto their web browser, such as uBlock Origin, which prevents advertisements from being loaded on webpages and can also help to prevent scareware.
Importantly, make sure to “avoid what is known as ‘the click reflex.’ In other words, ignore all unexpected pop-up ads, warnings about new viruses, or invites to download free software that is not from a trusted organization” (Fortinet). By avoiding “the click reflex”, you can save yourself a lot of trouble. If you are worried the pop-up is a legitimate notification from your antivirus, open your antivirus software through either the desktop icon or taskbar icon, not by clicking on the notification. On that note, it is good to keep in mind that “legitimate antivirus software, network firewalls, and web security tools will protect users from the spread of scareware” (Fortinet). Make sure that the antivirus software you have is legitimate and effective so that, if something does try to infect your machine, it can stop it before it is too late.
Resources & Further Reading
Crowdstrike. “Scareware: Definition Examples & How to Prevent It | CrowdStrike.” Crowdstrike.com, 2019, www.crowdstrike.com/en-us/cybersecurity-101/malware/scareware/.
Fortinet. “What Is Scareware? Defined and Explained.” Fortinet, www.fortinet.com/resources/cyberglossary/scareware.
IBM. “Scareware.” Ibm.com, 28 Mar. 2023, www.ibm.com/think/topics/scareware.
Malwarebytes. “What Is Scareware and How to Protect Yourself.” Malwarebytes, 10 Feb. 2025, www.malwarebytes.com/cybersecurity/basics/scareware.
Leave a comment